What’s new?
UPDATE: Jan. 27, 2023 – version 1.6.46
This is a maintenance release, which fixes an issue with the license upload form in certain browsers on Windows.
We also updated another third party component to the newest version, which fixes a security flaw that was found in that component.
Our engineers investigated any potential for a vulnerability in SlashDB from that component and determined that it is not possible to exploit that flaw. However out of abundance of caution we decided to not wait for the next planned release and included the update. You are advised to upgrade your SlashDB installations to the latest version.
Should you require a detailed technical explanation of either issue or need help with the upgrade please do not hesitate to contact our Technical Support team.
UPDATE: Jan. 6, 2023 – version 1.6.44
This is a maintenance release, which fixes a memory leak caused by a bug in a third party component.
The symptom is increased memory utilization over time and can occur with repeated requests to SQL Pass-thru queries rendered to JSON or XML formats. The root cause is in a third party component. This release contains a work around in our code that avoids triggering the problem. In the upcoming SlashDB ver. 1.7 we will use a newer version of that component, in which the underlying issue is already fixed.
UPDATE: Oct. 7, 2022 – version 1.6.43
This is a maintenance release with number for fixes and improvements including:
- Core – Handle invalid percent encoding values in URL
- MS SQL – Fix filter on very large values for the rowversion type in
- MS SQL – Fix HTTP 500 on stale connection
- MySQL – Display error message when database name not present in connection string override
- Snowflake – Handle Session timeout and token expiry
- Snowflake – Test connection hangup or too long timeout
- Snowflake – Fix connection string schema when connection string override is used
- Oracle – Enable connection with service name on database config and connection wizard screens
- Oracle – Move libaio dependency to the database package
- Security – Disable browser’s autocomplete feature for password field
- Security – Show warning when user is added with email address, which already exits
- Security – Add certain well known domains of identity providers to Content-Security-Policy
- Security – Show only valid IDPs in login page
- SAML – Add automated tests
- SAML – Autoconfiguration using metadata fetching
- SAML – Make error message box red
- SAML – Clarify message about invalid configuration of identity provider
- SAML, JWT/OAuth – auth.cfg validation fixes
- JWT/OAuth – Add more diagnostic logs
- GUI – Fix typo in error message for JSON schema minimum length.
- GUI – Fix missing button for on the database list screen for non-admin users
- GUI – Disable sorting buttons while query is executing
- GUI – Add checkbox to stream query results in Query Studio and SQL Pass-thru
- GUI – Generate valid database endpoint when database name not given
- GUI – Fix generating bad URLs for queries with a slash for parameter value in Query Studio
- Build – Remove redundant option ‘sqlalchemy_sdb.sqlpassthru.autocommit’ in slashdb.ini
- Build – Automatically generate md5 checksums file for dist
- Build – Allow for relative paths in the slashdb.ini file
SAML 2.0
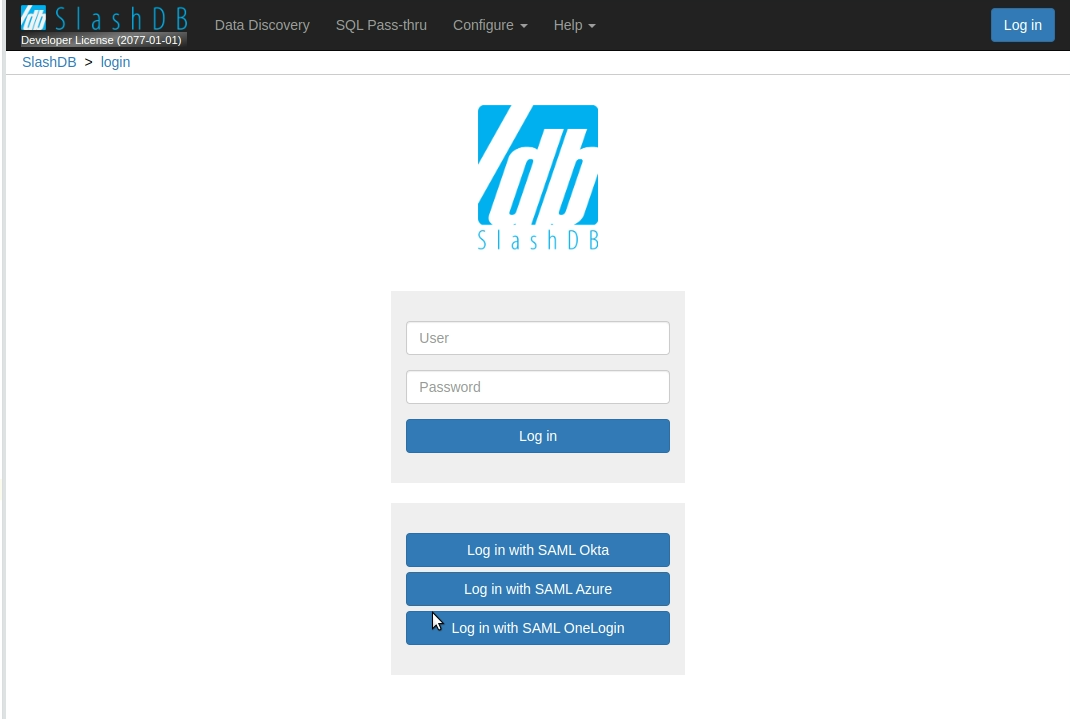
SlashDB Enterprise Edition now fully supports single sign-on under industry standard SAML 2.0 protocol. It’s now possible to configure both user interface and programmatic authentication using third party identity providers such as Azure Active Directory, Okta, OneLogin and many more.
Clients who need to authorize third parties to APIs (i.e. clients of their own) can leverage this feature to allow those end clients to self-manage authentication, including password resets, password strength, two-factor authentication and authentication policies.
With SlashDB Enterprise Edition, it is possible to configure multiple identity providers at a time. This allows for multi-tenant installation where the API owner’s identity is managed separately from each API clients’ identities. Each end-client can be greeted with their own login page, or all identity providers can be displayed on the same login page as shown in the screenshot below.
Please get in touch with us to discuss your specific requirements.
What’s improved?
Security
We submit SlashDB to penetration testing prior to each release. Although no major issues have been found, we’ve taken the time to address certain minor findings:
- Suppressed false alarm regarding email disclosure from automated scanner by using minified JavaScript code for AngularJS
- Updated jQuery and other JavaScript components to latest stable versions
- Hardened the NGINX configuration to lock out access to certain subdirectories
- Hardened certain file system permissions
User Experience
Various fixes and feature improvements including:
- Database setup wizard now has an option to override the connection string
- Clickable database names in the list of connected databases
- License page now clearly explains which license constraints might be invalid or expired
- Fixed URL bug in Data Discovery when primary key column contained an empty string
- Improved error reporting on failed login using OpenID Connect
Performance and Core Functionality
Of note are:
- Reflection of database models, which contain references to tables from other schemas
- Fixed issue with buffered streaming where database connection would not be returned to connection pool
- Fixed default values for certain data types in SQL Server
- Added support for ?count in Data Discovery
- Return HTTP 400 status for content types where ?transpose modifier is not allowed
- Code cleanup resulting from static code analysis
Documentation and Distribution Packaging
- Updated to latest database drivers where applicable
- Removed unused settings from slashdb.ini and added some beneficial ones
- Fixed path for model cache location
- Improved documentation on logging configuration, including support for Amazon CloudWatch and S3
- Improved documentation on Accept header
- Added certain missing paragraphs in documentation
Connect with us
We invite you to get in touch with us. You can reach us via:
- Gitter.im (chat room)
- StackOverflow (use tag “slashdb” to post questions)
- Contact form
Attribution
The “curious cat” picture on top is by Sereja Ris.